UPDATE 7th April 2020: Updated all Software Links to the latest.
UPDATE: 13th May 2017: A new ransomware has been identified known as Wannacry Ransomware, which has affected many countries in Asia, Europe, and America. It is a type of Encrypting Ransomware (hopefully, the least capable Ransomware, check the article to know more about Encrypting Ransomware) that only targets your files and encrypts them so that you cannot access it. If you are under attack, you can use the solution provided inside the article for Encrypting Ransomware.
The rate of computer viruses is increasing day by day with the emergence of new coding technologies. The latest and probably the biggest threat to the internet browsers is Malware termed ‘Ransomware.’ It is a virus that is continuing to become computer nightmares to date.
The funny thing is, most internet users these days are quite casual and unaware of the potential threats they could be into, from their browsing habits. Internet Trackers are already monitoring our online footprints and selling those data to advertising companies. And a lot of them deal with malicious practices.
You could be at the risk of getting infected with ransomware from simple activities such as downloading any file, especially torrent files, opening spam email links, and visiting unsafe websites. It is all in our browsing habits.
So, what exactly is this Ransomware? And How to Protect yourself from it?
In today’s article, I am going to discuss Ransomware in detail. I will make you aware of its working mechanism and tell you some of the easiest ways how to prevent cyber attacks and protect yourself from becoming a ransomware victim.
Also, if you are already under attack and reading this article, don’t worry. I will also discuss the necessary steps to recover back your files and your computer access.
Here’s an overview of the post:
Let’s start by discussing what exactly is ransomware.
 What is Ransomware?
What is Ransomware?
Well, as you have already guessed, Ransomware has something to do with ransom.
What is Ransom?
Ransom is a sum of money demanded by a kidnapper against the release of the kidnapped person.
Likewise, Ransomware is a Malware that encrypts all your computer files and software and demands money against your PC access.
Yes, that’s quite scary! 🙁
YOU MAY ALSO LIKE: How to start a Secret Conversation on Facebook Messenger?
And above that, this virus isn’t easy to defend. Yes, I am damn serious.
The virus will lock down your computer, and you cannot access any of the files or software installed.
The virus is coded in a way that attacks the system and takes control over it.
What’s more dangerous? Once it infects your system, even a powerful antivirus cannot recover the files for you. They can only remove the virus file at best, not the encryption.
To be exact, there is almost no process available to regain your ransomware-encrypted files in any way other than paying money and fulfilling their demands. (Notice I said ‘almost,’ because there are some limited ways available, which does not fully guarantee that it can recover 100% of your encrypted files, I will discuss them later in the article)
I guess you have got a decent idea about Ransomware by now and understood how fatal it could be.
If you keep your study materials inside your computer and don’t have any backups, then it will be a nightmare if you face a Ransomware attack at night just before exams.
No matter how hard you scream, nobody is going to help you out if you ever fell into this ransomware trap.
Is paying Ransom a Solution?
This might be necessary for someone who has some valuable documents inside their computer hard drive. You may want to spend the money desperately.
But, is paying the ransom safe? Should you pay them money to get back access to your computer?
The answer is a big ‘NO.’
There are reasons behind this.
Firstly, it is unethical and illegal in most countries (if not all, I am not sure about laws in all countries). If you pay them money, then, indirectly, you are supporting those people who are taking the money, and hence, you are committing a cybercrime.
Additionally, you are proving the criminals that this method of taking money works, and hence they will continue to infect other people like you.
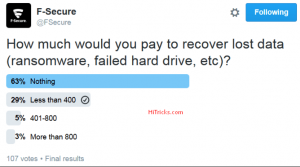
Secondly, the sum of money is well above your expectations. Most of the Ransomware asks payments in the form of bitcoins, the universal anonymous currency, where you cannot know the details of the other party, and you just transfer money using the bitcoin address. Now, the value of bitcoins is immense, and regarding local currency, it is going to burn your pockets.
The amount of ransom can be any amount from 100$ to 1000$ or even more.
Thirdly, even if you pay the price somehow and hope for getting your access back, there is no guarantee at all that they will keep their word and give you access. Because it is malware and controlled by them, they have the power to do anything they want. Suppose you pay ransom to a kidnapper, it does not guarantee that the kidnapper will release the captive, does it?
Hence, paying upfront is not at all an intelligent act.
So, now the question comes to safety. How can you save yourself from such a devastating ransomware virus attack?
Ransomware: Preventive Measures:
In this section, I will discuss the necessary precautions that you should take to avoid being hunted by Ransomware.
If you are already under attack, please refer to the next section, “What to do if I am attacked?” below.
They say an ounce of prevention is worth a pound of cure. So, it is worth that you follow the simple methods to get yourself out of reach of Ransomware.
It is the game of keeping your eyes open and thinking twice before you take action.
Block the path between you and the Ransomware:
Ransomware attacks are all through the internet. So, try to block the path between your computer and the Ransomware.
Find out the connecting links between the internet and your PC.
Check up your Internet Downloads:
The first connecting link is your Internet Downloads. Whenever you decide to download a file from the internet via your web browser, you are risking your PC to getting infected.
So, always do a pre-check up to ensure you are downloading files from trusted sources.
If you are a torrent lover, then always download torrents from verified websites. Try to read reviews before downloading a torrent file.
I have often found fake movie torrents with the file extension .exe after the movie name. That is an executable file and not media, and if you execute that file, nobody knows what will be carried out by the software.
Downloading files from 3rd party file-hosting sites are another source of ransomware infection. Usually, they try to fool you by placing ads over the ‘Download Now’ button, and there are fair chances that you will click on that ad and end up downloading malicious software.
My last friendly suggestion in this regard will be to stop downloading p**n. Most of those sites bundle Ransomware with the videos they provide for download.
You will get fooled easily because of your attractions!
YOU MAY ALSO LIKE: Download and Root Bluestacks 2 with Kingroot Trick
Don’t visit a link just because you are asked to:
Just because you received a link on your email or got an SMS with a link, it does not mean you should visit the same.
 Those old days of ‘You won a lottery’ type of spam are gone forever. Nowadays, spams are more surprising, and if you can’t differ between a real and a spam mail, you are ruined.
Those old days of ‘You won a lottery’ type of spam are gone forever. Nowadays, spams are more surprising, and if you can’t differ between a real and a spam mail, you are ruined.
Got an email saying Win a Galaxy S7 Edge for Rs200 only blah blah blah blah? Don’t visit those links.
They will usually trick you into downloading their Ransomware and asking you to open the file on your computer. When you do that, you are infected.
YOU MAY ALSO LIKE: [Guide] How to Dual Boot Remix OS with Windows [UEFI / Legacy]
Triple Check your Email Attachments:
This is another weak connecting link between your computer and the internet, which is often ignored by a lot of people.
Ever received an email that you think does not belong to you?
Then I suggest you do not open any attachments that come with it.
Common Spam-Mails include:
- An Order Receipt from a Marketplace
- Delivery Confirmation of some product
- A Tracking Number from an Order
- Domain Expiring in a week
- A Mail asking you to be present in High Court on a specified date
All these emails will seem very surprising to you and will contain attachments along with it.
They will try to make you open the attachment to know further details.
I suggest you refrain from such acts.
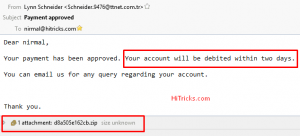
Here’s an example screenshot from an email I received.
The mail says my payment is approved, and my account will be debited within two days.
Whoa! What’s that shit?
I didn’t make any payments to anyone.
So, most likely, I am going to check the attachment below to find out the details of my payments.
And once I download the attachment and open it, I am under attack!
YOU MAY ALSO LIKE: 5 Alternatives to Google Play Store: Get Paid Apps for Free
Use an Antivirus Software:
Antivirus software is a must for every internet browser. And when I tell antivirus software, I don’t mean the Windows Defender shit that comes with your computer inbuilt.
Windows defender is just an essential software designed to protect you from some known malware only. It is not at all a good option for long-term protection from new virus threats.
For that, you need to install a 3rd party antivirus software.
So, any 3rd party antivirus will protect you from Ransomware?
The answer is ‘NO.’ Not all antivirus programs can protect you against Ransomware.
And above that, you need an antivirus that can protect you against all other malware and not just Ransomware.
I will not give you a list of antivirus software, but I will provide you with only two names, one free and another paid software, which tops the chart for both general malware protection as well as Ransomware.
Free Antivirus: Avast
First things first. I am using Avast Free Antivirus.
The reason I like them is that apart from protecting me from all threats, they never overload my system.
According to AV-Test, they are in 2nd position after Ahn Lab, which ranks first.
Let me tell you; their antivirus program is completely free. They have upgrades available for extra features like firewall, sandbox, etc.
You may consider upgrading Avast to the paid version if you need those extra features. But their powerful antivirus is always free. (Yet it ranks second in AV-Test, quite promising indeed)
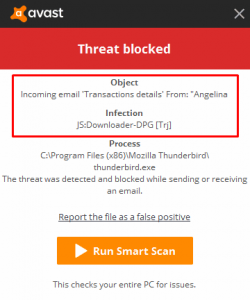
Check the below screenshot on how Avast protected me from a Trojan that was delivered to me in an email attachment.
YOU MAY ALSO LIKE: SECRET Trick to Play Soccer on Facebook Messenger
Paid Antivirus: Bitdefender
I had used Bitdefender for some months when they ran a promotional offer to provide free access to their software. And I liked it.
The reason?
It never disturbs you.
Yes, you heard me right. Once you install it and set it up and configure it correctly, it will do its job in the background automatically, and quarantine the infected files.
And it never fails.
The memory usage is low to medium. And the security is best in class. Consider using them if you want the maximum protection.
Backup your files Regularly:
Ransomware will target the data and software in your system. So it is best to keep them backed up so that you never miss them.
YOU MAY ALSO LIKE: Step by Step Tutorial: How to get Blue Verified Badge on Twitter?
 Backup your Documents and Media:
Backup your Documents and Media:
The best way to protect what you own is to make a copy of those and save somewhere away from the reach of the internet.
The best way is to backup them to an external hard disk.
External Hard Disks are becoming useful day by day. I won’t go into more detail here, but make sure your disk space is double the space of your internal memory of your computer.
So, if you have 500GB memory, grab a 1TB Hard Disk, at least. If you have 1TB memory, grab a 2TB Hard Disk, and so on.
Now the next thing is to back up your essential files. You can use Free Software like Todo Backup to Backup Everything on Windows.
Always run a backup every week. This will help you in the long-term.
YOU MAY ALSO LIKE: Error-Free Guide to Setup Facebook Instant Articles on WordPress
Backup Windows OS:
Ransomware infects at the system level. Hence you lose access to your system. To restore it, you need a complete backup of your Windows OS.
First things first, when you buy a new laptop or computer, they will either give you a windows recovery disk or ask you to create the recovery disk on new windows with software manually.
Do that and keep that recovery disk with you always.
Next, buy a 16GB Pen Drive and install the Windows OS there and make it a bootable pen drive. Keep it aside so that you can boot windows from the Pen Drive in times of need.
You can check out this article by Windows Central to Make a full backup of your Windows.
This will ultimately become your life savior.
 Awareness is Important:
Awareness is Important:
Remember, something you downloaded from the internet is still safe unless and until you open the file. So, even after you download some files, always make sure it is the right file you need to access. Then only open it.
How to Activate Dark Mode on Whatsapp?”]Ransomware: What to do if I am attacked?
So, until now, I was speaking of preventive measures for Ransomware Attacks.
But I know most of you won’t care about these points until you face one yourself.
So, if you came here looking for ways to recover your PC, which is under the control of Ransomware, then I won’t disappoint you either. I just want to say that your options are very very limited in what you can do.
Never Pay the Money:
Don’t Fall for Ranscam:
Heard of Ranscam?
No?
Well, let me elaborate on the term. Ranscam is when you pay money to the Ransomware owners but still don’t get back the access to your files.
Always remember, they hacked your computer for the sake of earning money. So, what makes you think that they will give you back the files after they get the sum of money?
They are hackers. Not your shopkeeper.
So never try to pay the amount.
Examine the Type of Ransomware:
Among the several types of Computer Ransomware, the following can be distinguished easily.
- Encrypting Ransomware
- Lockscreen Ransomware
- MBR Ransomware (Master Boot Record Ransomware)
The encrypting Ransomware will just encrypt all your files on your computer, but won’t block your access to your PC system.
You can visit all your folders and files. They will be encrypted with a different extension.
 The Lockscreen Ransomware will block access to your files and show a lock screen with the ransom message.
The Lockscreen Ransomware will block access to your files and show a lock screen with the ransom message.
The MBR Ransomware, the worst of all, modifies the MBR of your computer and prevents your OS from booting and shows the ransom message on the black screen.
Depending on the type of Ransomware, you need to take appropriate steps.
However, let me tell you, there is no guarantee that you can recover 100% of all your files, but at least you can try.
YOU MAY ALSO LIKE: How to Become a Google Local Guide and Get Rewarded?
For Encrypting Ransomware:
These are the most common types of Ransomware, and there are more chances that the Ransomware you got infected with is encrypting ransomware.
Thanks to a lot of helpful developers on the internet, some ransomware-encrypted files decrypting software tools are available right now.
However, these tools will only work if your Ransomware is an Encrypting Ransomware that won’t block access to your computer, just change the file type to encrypted type. It won’t work for Lockscreen or MBR Ransomware.
Well, note that computer security experts develop the Ransomware, so they always keep updating to the latest binaries. These decrypting software are updated with the latest binaries after the developers come to know of new developments.
So, the software can only decrypt encrypted ransomware files of some known algorithms. If you are under the control of a new and highly secured ransomware, this software won’t work.
Still, you can give them a try.
The names, download links, and instruction files to the software are provided below:
- Wildfire Decrypter: Download | Instructions for Using
- Rakhni Decrypter: Download | Instructions for Using
- Shade Decrypter: Download | Instructions for Using
- Coinvault Decrypter: Download | Instructions for Using
- Rannoh Decrypter: Download | Instructions for Using
- Xorist Decrypter: Download | Instructions for Using
The instruction files are written in a very lucid way; I will recommend you to follow the instructions and continue with the file decryptions.
Note:
- Remove the ransomware malware file before starting the decryption. Else the Ransomware will again encrypt it.
- The decryption process is very long and can take several hours to several days. Be patient, and wait for it. Do not close or reboot the computer in between the process.
Keep your fingers crossed.
A list of more Ransomware Decryptors has been listed by TheWindowsClub Here.
For Lockscreen Ransomware:
As you can already understand by now, that the Lockscreen Ransomware won’t let you access the computer, and you need first to remove the Ransomware before you can get access to your files.
Again, after you get access to your files, you need to decrypt them if they are encrypted.
So this is a two-step process, the first of which you need to remove the Ransomware.
So how can you do it if you can’t access your computer?
Well, there is a way to do that.
You need a different computer and a bootable USB stick for that. You need to download the malware removing the program on your PC, create the bootable USB stick and use that to boot your computer.
A complete guide on how to do that is written here. You can follow the same.
YOU MAY ALSO LIKE: Blogosphere: Boost your Facebook Traffic by 500% for FREE
Use the TrendMicro Lockscreen Ransomware Removal Tool:
Trendmicro has released a ransomware removal tool specially made for lock screen ransomware. Visit their website to view and download the tool.
So, your first step in removing the Ransomware is done.
Now you need to see if your files are encrypted, and if so, decrypt your encrypted data.
Follow the recommended steps under the encryption ransomware section to decrypt them.
For MBR Ransomware:
Brace Yourselves! They are the worst kinds of Ransomware available on the internet. They f**k up your computer along with your files.
What they do is modifying or deleting your boot record, thus preventing your os from booting.
Sounds spooky?
Well, it is. Seriously, the last thing you want to be a victim of is an MBR Ransomware.
Just a random warning, if you are a torrent fan, and see a media file with an extension .exe in the downloaded torrent, then immediately delete it, don’t ever think of running them. They are Ransomware.
Now coming to what you can do in case you are under attack.
You may cry, but unfortunately, nobody is going to listen. So, you need to take steps.
The bad news is you can’t get any part of your computer back. It is gone forever. That’s why we say keep backups repeatedly.
You need to wipe your hard disk completely, and as well as flush off your operating system, no part should be left out.
You will need the Windows installation CD to install the recent version of windows.
Spyware Techie has an excellent article on how to remove the Ransomware and freshly install your windows. Note that the article is written on Petya Ransomware, which is a highly dangerous MBR Ransomware, but the removal steps are the same for every MBR Ransomware. You can read it here.
YOU MAY ALSO LIKE: SECRET Trick to Play Basketball on Facebook Messenger
Use MBR Filter Software to prevent MBR Ransomware:
After you successfully remove MBR Ransomware and freshly install windows, don’t forget to install MBRFilter Software. It is a highly specialized software that keeps your MBR in read-only mode and thus preventing the Ransomware from modifying your MBR in the future. So, this software acts before the attack; it can’t protect you if you are already the victim.
Check out the details of MBR Filter and instructions for using the software along with the Download Link from here.
Last Words:
Thanks for reading this informative post on Ransomware and their removal techniques. I hope all your questions and confusions regarding Ransomware are clear by now.
I have tried to answer all types of questions regarding Ransomware in this single article.
Before ending my post, I want to remind you again; that awareness is an essential quality necessary to stay safe from ransomware attacks.
Don’t visit malicious links or download files from websites you don’t trust.
Even if you have already downloaded some files from untrusted sources, you are still safe as long as you don’t open the file. Keep your eyes open. Don’t fall for attractions that seem impossible.
YOU MAY ALSO LIKE: Premium Tricks by IftiSEO (PTI): The Best Bloggers Community
BONUS: Use sandbox for opening untrusted downloaded files:
Say you downloaded a file from an unknown source that you don’t trust. Still, you want to open that file, then use the sandbox to quarantine the file and open it in a confined space away from the rest of your computer’s data.
Sandbox is a paid upgrade available in Avast Antivirus. Upgrade your avast free subscription to Avast Internet Security and Avast Premier to get this Sandbox feature where you can isolate a file and open it.
This will shield you against bad Ransomware as they can’t get into your system.
Mind Sharing the Article?
Don’t let your friends become the victim of Ransomware again. Use the social share buttons to share this post with your friends on Facebook and Twitter.
Sharing does not cost money but can save a whole bunch of money to your friends, and it also helps us to grow.
Have any queries? Want to appreciate it? Fire them up in the comments section below.
I will be waiting to hear from you. 🙂
Defeat Ransomware with Confidence!
Tags: antivirusransomware
Nirmal Sarkar is a Biotechnologist from the city of Joy, Kolkata. He is the founder of this blog and covers a wide range of topics from Gadgets to Software to Latest Offers. You can get in touch with him via nirmal@hitricks.com







Hi there, my friend’s PC was affected by Ransome, and I’m taking every step possible to prevent this. I’ll soon get an external HDD for backup. Thanks mate for sharing your tips on preventing this deadly attack.
You are most welcome buddy. Glad to know that I could be of help. Keep visiting HiTricks.
Unfortunate, my old PC was affected by Ransome. All my files got encrypted and I kinda lost them all. I have no hopes for getting them back though.
I’m taking precautions much better on my newer system, and I already started taking regular backups, you never know how you get attacked. Basically, the last time, I turned off my PC, and when I turned on my PC on the very next day, my wallpaper had changed with a message from the hackers, and also each folder had 3 files – 1 .html and 1 .pdf and another MS Word file which containing the same message, about paying $500 to unlock my files.
Well, I’m doing nothing with it, and all my files are gone for good. 🙁
This thing is very painful. But you may try going through the ransomware decryptors. Let me know if those tools worked. Thank you.
Great article bro….you covered everything in this article….thanks for the information.
You are most welcome Adarsh.
thanks for the information, loved the way you explained , i will definetely recommend this site to my friends.
Thank you very much Surendra 🙂
.___. Awesome
Thank you Rejul for leaving your valuable comments. 🙂